These tips may not be for you. Do you only use software and devices approved by your organisation? Do you always install software updates as soon as they appear? Have you long since changed the default password for your home router to something no one is ever going to guess? Do you avoid public Wi-Fi networks like the plague?
If your answer to all these is a confident ‘yes’, you are all set. On behalf of all security professionals: thank you for keeping it safe!
If, however, you don't quite recognise yourself in the above, you’d better have a look at the following helpful best practices for safe remote working.
Tip 1 | Only use company approved devices and tooling
Only use pre-approved tooling, services, and devices. Applications that are not pre-approved or facilitated by your organization may contain security or privacy vulnerabilities.
Tip 2 | Be vigilant about your devices
Do not leave your work devices unattended in a freely accessible public area or in your car. Do you have to leave your device unattended at your workplace? Press Windows key + L on a Windows device, or Control + Command + Q on a Mac, to quickly lock your screen.
When working from home, ensure your network is properly protected from unauthorized access. This starts with changing your router’s factory settings. The default login credentials of your router are usually printed on the bottom or back of your router or in a manual, and are often disclosed on the public internet. Finding default login credentials is trivial for any cybercriminal. Oh, when setting a password, make sure it’s a strong one!
Tip 3 | Avoid public Wi-Fi
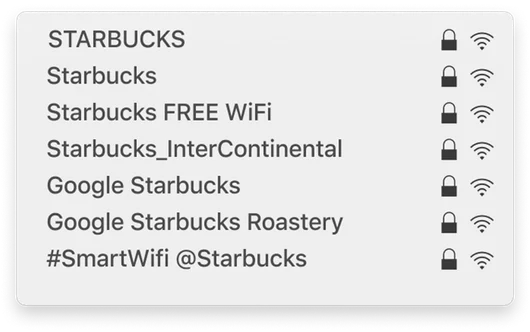
Avoid connecting to public Wi-Fi networks. A public network is often not password protected (they are missing the signature padlock next to their name). Everyone can connect to this network, including, of course, cybercriminals. The key concern with public Wi-Fi is that it's often less secure, making it easier for cybercriminals to intercept data transmitted over this network.
Another example is that cybercriminals can set up fake Wi-Fi hotspots with names similar to legitimate networks, unknowingly tricking you into connecting to them instead.